我已经为我的web服务器(Apache)和WebSocket服务器(PHPWS)安装了let's Encypt(https://letsencrypt.org/)证书。问题是SSL WebSocket在Firefox上运行良好,但在Chrome、Chromium和Opera上却无法运行。我以前尝试过自签名证书和安全WebSocket在Chrome和Chromium中工作。
我的网页位于https://warsoftheheroes.eu
登录名:zosia,密码:zaqwsx
这是您登录时应该在Chrome javascript控制台中看到的内容:
WebSocket connection to 'wss://warsoftheheroes.eu:1025/chat' failed: WebSocket opening handshake was canceled websocket.js?v=20170506:4
WebSocket connection to 'wss://warsoftheheroes.eu:1025/main' failed: WebSocket opening handshake was canceled websocket.js?v=20170506:5
这是我在WebSocket(PHPWS)服务器日志中看到的内容:
PHP Warning: stream_socket_accept(): Failed to enable crypto in [some path].../vendor/devristo/phpws/src/Devristo/Phpws/Server/WebSocketServer.php on line 126
Warning: stream_socket_accept(): Failed to enable crypto in [some path].../vendor/devristo/phpws/src/Devristo/Phpws/Server/WebSocketServer.php on line 126
PHP Warning: stream_socket_accept(): accept failed: Success in [some path].../vendor/devristo/phpws/src/Devristo/Phpws/Server/WebSocketServer.php on line 126
Warning: stream_socket_accept(): accept failed: Success in [some path].../vendor/devristo/phpws/src/Devristo/Phpws/Server/WebSocketServer.php on line 126
[某些路径]是我添加的,而不是真正的路径
会有什么问题吗?证书在HTTPS上使用Apache,但无法在WSS上使用WebSocket。
-=E D I T=-
这是我的Apache SSL配置:
SSLCipherSuite ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES128-SHA256:ECDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384
-=编辑2=-
openssl更新后有nmap的输出:
nmap --script ssl-enum-ciphers -p 443 warsoftheheroes.eu
Starting Nmap 7.40 ( https://nmap.org ) at 2017-05-10 18:44 CEST
Nmap scan report for warsoftheheroes.eu (81.163.204.80)
Host is up (0.013s latency).
rDNS record for 81.163.204.80: pppoe-static-a-80.interblock.pl
PORT STATE SERVICE
443/tcp open https
| ssl-enum-ciphers:
| TLSv1.0:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A
| TLS_DHE_RSA_WITH_AES_128_CBC_SHA (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: server
| TLSv1.1:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A
| TLS_DHE_RSA_WITH_AES_128_CBC_SHA (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: server
| TLSv1.2:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (secp256r1) - A
| TLS_DHE_RSA_WITH_AES_128_GCM_SHA256 (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_256_GCM_SHA384 (dh 2048) - A
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (secp256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (secp256r1) - A
| TLS_DHE_RSA_WITH_AES_128_CBC_SHA256 (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_128_CBC_SHA (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA256 (dh 2048) - A
| TLS_DHE_RSA_WITH_AES_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_AES_128_GCM_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_GCM_SHA384 (rsa 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_256_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| TLS_DHE_RSA_WITH_CAMELLIA_128_CBC_SHA (dh 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: server
|_ least strength: A
而且
nmap --script ssl-enum-ciphers -p 1025 warsoftheheroes.eu
Starting Nmap 7.40 ( https://nmap.org ) at 2017-05-10 19:07 CEST
Nmap scan report for warsoftheheroes.eu (81.163.204.80)
Host is up (0.015s latency).
rDNS record for 81.163.204.80: pppoe-static-a-80.interblock.pl
PORT STATE SERVICE
1025/tcp open NFS-or-IIS
| ssl-enum-ciphers:
| TLSv1.0:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (brainpoolP256r1) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: client
| TLSv1.1:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (brainpoolP256r1) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: client
| TLSv1.2:
| ciphers:
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 (brainpoolP256r1) - A
| TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 (brainpoolP256r1) - A
| TLS_RSA_WITH_AES_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_128_CBC_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_128_GCM_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_AES_256_CBC_SHA256 (rsa 2048) - A
| TLS_RSA_WITH_AES_256_GCM_SHA384 (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_128_CBC_SHA (rsa 2048) - A
| TLS_RSA_WITH_CAMELLIA_256_CBC_SHA (rsa 2048) - A
| compressors:
| NULL
| cipher preference: client
|_ least strength: A
如果您检查Chrome内部,并在插座尝试连接时开始录制,您将看到以下内容:
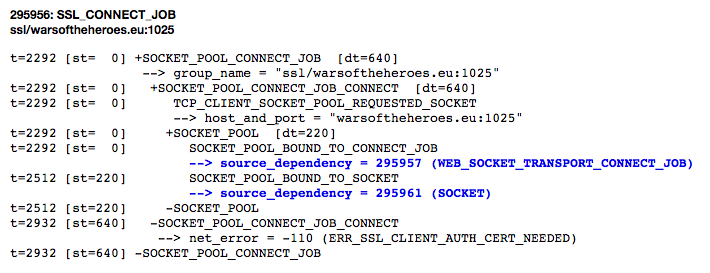
err_ssl_client_auth_cert_needed非常明确,告诉我们您的证书有问题。
通过查看它,我们可以看到您正在使用RSA,这是一种过时的密钥交换。相反,您应该使用DHE_RSA或ECDHE_RSA。即使https没有问题,但这可能是建立安全websocket连接的一个问题,请确保使用了强密码和密钥交换机制。
还有一个非常基本的问题是,phpws进程没有对证书/pem文件的读取权限,证书已过期。所以你可能也要再检查一下,以防万一。